Managed service providers exist to simplify how organizations run their infrastructure. They hold administrative credentials, maintain persistent network connections, and operate remote management tools with unrestricted access to client environments. For the organizations that hire them, this is an operational convenience. For APT10, a China-based threat actor also tracked as Red Apollo, it was an attack vector.
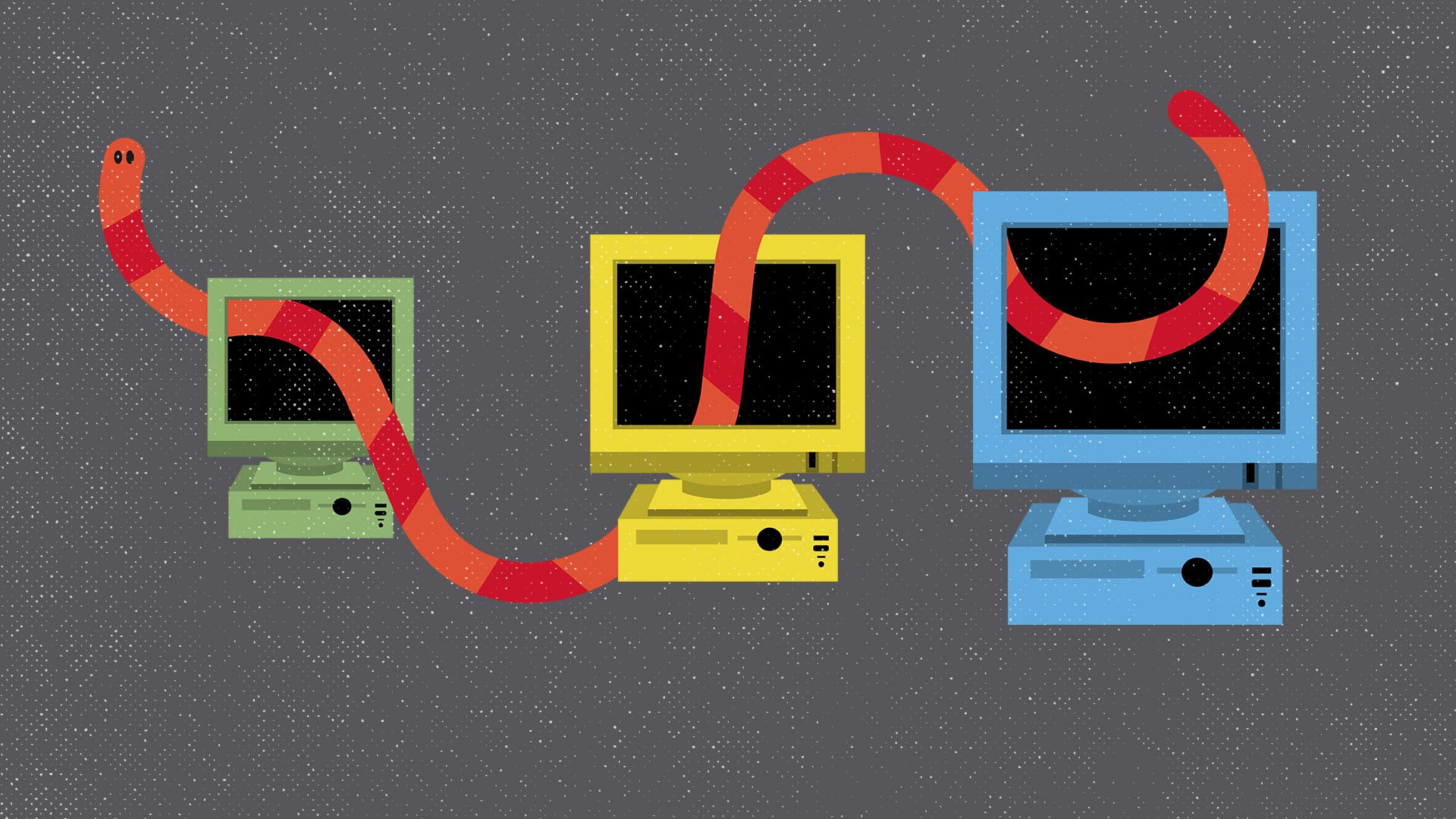
Between 2014 and 2018, APT10 ran a sustained campaign against MSPs across twelve countries. The group did not need to compromise its actual targets individually. It compromised the companies that had trusted access to all of them simultaneously. The operation became known as Cloud Hopper, named for the lateral movement APT10 conducted across client environments using MSP infrastructure as the channel.
One Compromise a Thousand Targets
PwC UK and BAE Systems first documented the campaign in a joint report published in April 2017, describing it as one of the largest sustained global cyber espionage campaigns they had ever observed. Their analysis identified APT10's activity patterns as consistent with China Standard Time and noted that the group's targeting priorities closely matched the strategic interests associated with China-based state activity at the time. The sectors hit were not random. Aviation, satellite technology, maritime systems, industrial automation, banking, telecommunications, pharmaceutical manufacturing, and oil and gas exploration were all targeted across multiple continents over several years.
The strategic logic behind targeting MSPs rather than end organizations was straightforward. MSPs maintain the kind of privileged, persistent access that would take months to establish through direct intrusion. By compromising one MSP, APT10 inherited access to every client network that MSP administered. The BAE Systems threat research team, writing alongside PwC, noted that successful global MSPs are particularly attractive targets precisely because they become a hub from which an attacker can reach multiple end-victim networks from a single foothold.
Getting In Without Breaking In
The entry technique was not sophisticated by the standards of state-sponsored intrusions. APT10 used spear phishing campaigns to deliver custom malware including PlugX, RedLeaves, and QuasarRAT into MSP environments. Once inside, the group used the MSP's own administrative tools and stolen legitimate credentials to move laterally into client networks. The PwC and BAE Systems technical annex documented this methodology in detail, showing how APT10 progressed from initial tactical malware for reconnaissance and credential harvesting to sustained malware like PlugX for long-term access.
From the client's perspective, the access looked like routine MSP activity. There was no anomalous traffic signature to detect because the attacker was using the same tools and credentials the MSP used every day. Carnegie Mellon's Software Engineering Institute analyzed this visibility problem directly in its case study of the operation, noting that because cloud service providers manage the Identity and Access Management layer on behalf of their customers, clients are structurally unable to monitor when an attacker pivots within the provider's infrastructure to reach a different client system. The shared responsibility model that makes cloud service delivery commercially viable is the same model that made Cloud Hopper structurally difficult to detect.
A Shopping List Disguised as Espionage
The scale of what APT10 accessed over four years has never been fully disclosed. The German Marshall Fund's Securing Democracy project, which tracks state-linked cyber incidents, identified confirmed or probable targets including Brazilian mining giant Vale, biotech firm Syngenta, and Swedish telecoms company Ericsson, each with clear strategic relevance given China-aligned commercial interests during that period.
At least eight of the world's largest MSPs were affected, including Hewlett Packard Enterprise and IBM, according to reporting by Bank Info Security drawing on a Wall Street Journal investigation. The full picture remained obscured for years because MSPs were reluctant to confirm to their clients whether they had been compromised, concerned about reputational damage. One investigator told the Wall Street Journal that mapping the campaign's true scope was like trying to pin down quicksand. The US government confirmed that APT10 stole personnel records belonging to more than 100,000 US Navy personnel as part of the broader operation.
Five Governments Named the Actor
In December 2018, the US DOJ unsealed an indictment against two individuals, Zhu Hua and Zhang Shilong, alleged members of APT10 operating out of China, charging them with conspiracy to commit computer intrusions, wire fraud, and aggravated identity theft. The indictment alleged that the two had breached networks belonging to more than 45 technology companies and US government agencies across at least a dozen states. FBI Director Christopher Wray, speaking at the announcement, described the list of victim companies as reading like a who's who of the global economy.
The indictment triggered a coordinated international response that had no precedent in scope. The governments of Canada, Australia, New Zealand, and the United Kingdom jointly attributed the campaign to China's Ministry of State Security, marking only the second time the Five Eyes alliance had collectively attributed a cyberattack to a specific nation state. Japan issued a separate statement confirming sustained attacks against private companies and academic institutions on its territory. The UK's National Cyber Security Centre had already issued an advisory in April 2017 telling organizations not to accept assurances from their MSPs at face value and to demand evidence instead.
Neither Zhu nor Zhang has been arrested. The US does not have an extradition treaty with China, and APT10 continued operating after the indictments, shifting its tooling from Cloud Hopper-era malware to more sophisticated custom backdoors and refocusing its targeting rather than standing down. As Dark Reading noted in its analysis of the indictments, the charges established a public record and a multilateral attribution precedent, but their practical impact on APT10's operations was limited.
The Logic That Has Not Changed
Operation Cloud Hopper demonstrated something the interview above puts in contemporary terms: the highest-value target is rarely the one you attack directly. It is the layer of trust and privileged access that sits between the attacker and everything they want to reach. In 2014, that layer was the managed service provider. In 2026, it is the cloud control plane, the administrative layer governing identity, access, and resource provisioning across cloud environments at global scale.
The attack surface has shifted. The operational logic behind it has not. APT10 did not need to breach a hundred individual organizations. It needed to breach the one entity that had trusted administrative access to all of them. An attacker targeting cloud infrastructure today faces the same calculus. Compromising the control plane that governs everything beneath it is more efficient, more consequential, and harder to detect than targeting individual workloads. The scale of the consequence follows directly from the position of the target in the trust chain. That is what Operation Cloud Hopper established, and it is what makes the control plane the most consequential attack surface in modern cloud security.
Primary sources
PwC UK and BAE Systems joint report, April 2017; US DOJ indictment, December 2018; FBI APT10 wanted page; UK NCSC advisory, April 2017; CCDCOE Cyber Law Toolkit)