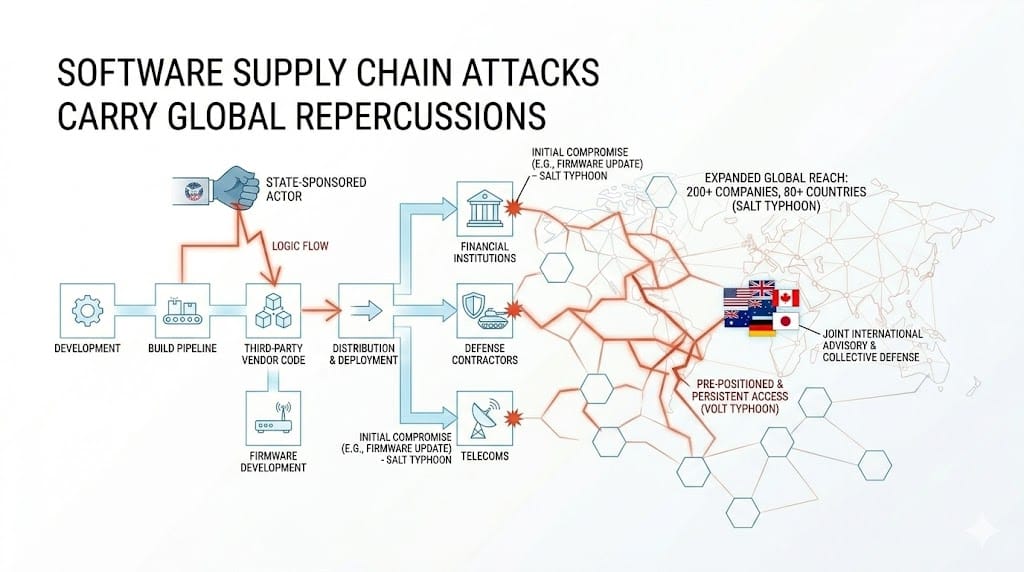
For a long time, the mental model for a nation-state cyberattack looked like a direct assault where a government-backed group picks a target, breaks through its defenses, and extracts what it came for. But that model is quite outdated. What state-sponsored actors figured out is that the most valuable targets in the world, the telecoms, the defense contractors, the financial institutions, are also the hardest to breach directly. So they stopped going through the front door and started going through the suppliers, the build tools, the third-party vendors, and the software pipelines that every organization trusts completely and audits almost never.
The shift has been visible in the campaigns that security agencies have spent the last several years trying to contain. Salt Typhoon, a threat group attributed to China's Ministry of State Security, did not penetrate eight major US telecommunications providers by breaking encryption or outgunning their security operations centers. It got in through known vulnerabilities in routers and firewalls, the unglamorous edge infrastructure that sits just outside the spotlight of most enterprise security programs. And once it was in, it stayed. Because organizations that were not designed around the assumption of persistent internal threat had no mechanisms to find it, let alone evict it. By the time AT&T and Verizon confirmed containment in late 2024, the group had already expanded its reach to over 200 companies across 80 countries, according to the FBI's August 2025 assessment.
Volt Typhoon told a similar story from a different angle. Rather than focusing on intelligence collection, this group pre-positioned itself inside US critical infrastructure, including energy, communications, transportation, and water systems, and maintained that access for more than five years without being detected. CISA, the FBI, and the NSA have all confirmed that the objective was not immediate disruption but strategic positioning, the ability to cause catastrophic failures at a geopolitically convenient moment. That is warfare conducted through software.

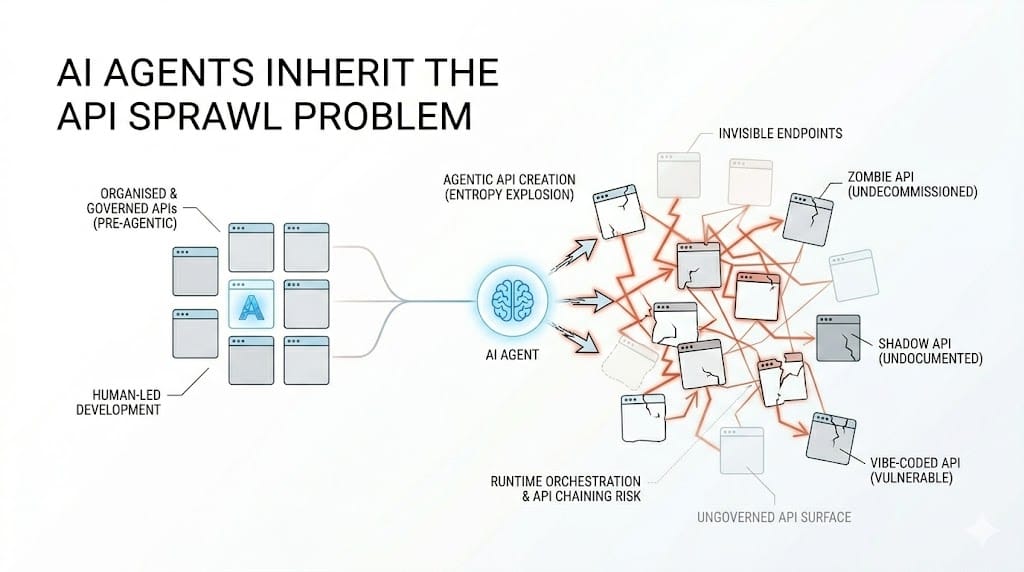
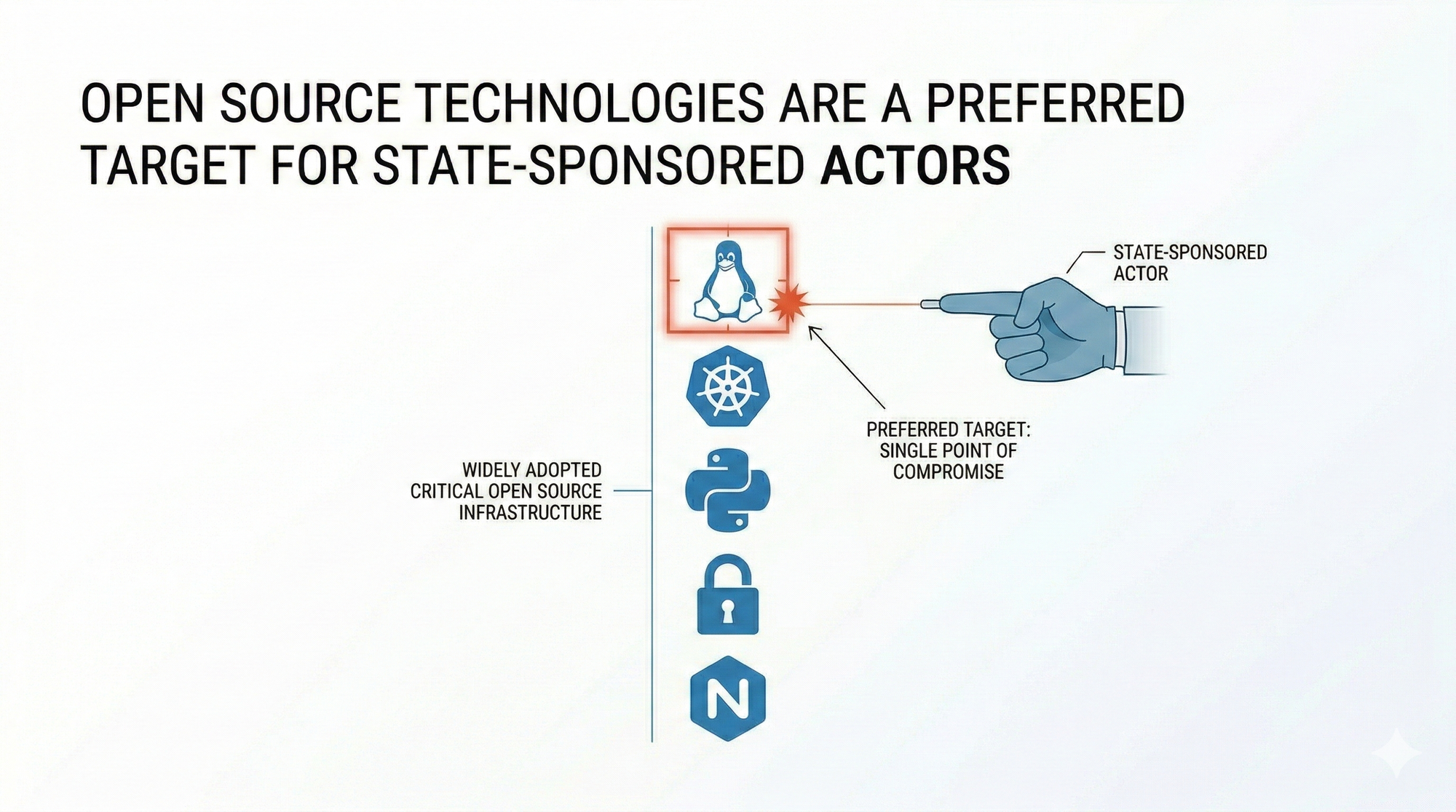
What makes the supply chain such an attractive vector for state-sponsored actors is the same thing that makes it so dangerous to defend. Every organization depends on a web of third-party code, external services, and automated build pipelines that carry enormous levels of inherent trust across the stack. A developer's laptop, a cloud-hosted CI/CD tool, a router firmware update, none of these are obvious targets from the outside but each one is a plausible entry point for an adversary patient enough to wait for the right moment. And nation-state actors, by definition, have that patience. They are not trying to make money by Friday. They are executing against decade-long strategic objectives.
The international dimension of the supply chain problem extends well beyond the United States and its telecommunications infrastructure. The Salt Typhoon advisory published jointly by the FBI, NSA, and CISA in August 2025 was co-signed by intelligence and law enforcement bodies from Australia, Canada, Germany, Japan, and the United Kingdom, which is a significant signal in itself. A joint advisory of that breadth does not get issued because one country's networks were compromised. It gets issued when allied governments have collectively concluded that the threat is systemic, that the attack surface is shared infrastructure, and that no single nation's security posture is sufficient to contain an adversary operating at this scale across this many jurisdictions simultaneously. The Five Eyes intelligence community treating a software supply chain campaign as a collective defence matter is a definitional shift in how state-sponsored cyber activity is classified and responded to.

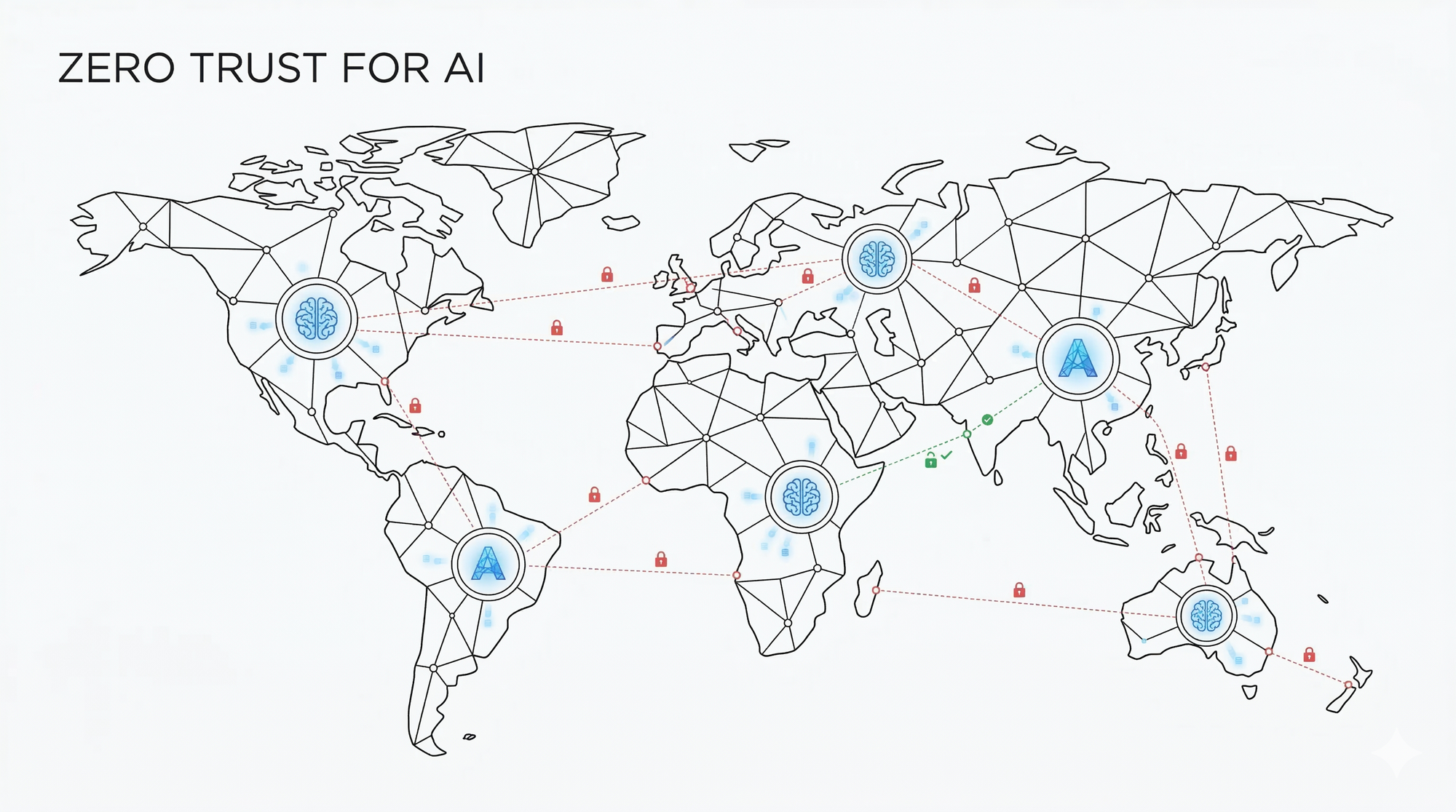
The industries paying the steepest price are the ones that believed their perimeter was their protection. Telecommunications, government contractors, and defense-adjacent technology companies all learned the same lesson at significant cost, which is that an environment secured at the edge and trusted internally is an environment that cannot detect or contain an adversary who is already inside it. Supply chain attacks succeed specifically because they exploit that trust, and the organizations that have reduced their exposure are the ones that stopped extending it automatically. The security teams making real progress are treating every pipeline, every build agent, and every vendor connection as a potential threat surface rather than a safe zone, which is exactly the architectural posture the Zero Trust model demands.
The governance dimension is where this challenge becomes most difficult to address at the international level. Software supply chains do not respect national borders. A router manufactured in one country, running firmware developed in another, deployed inside critical infrastructure in a third, and managed remotely through a vendor in a fourth, is not an unusual configuration. It is the default. The question of who is responsible for verifying the integrity of each layer in that chain, which government has jurisdiction to mandate it, and what accountability mechanism exists when a vendor fails to patch a known vulnerability for years, has no clean answer under existing frameworks. Salt Typhoon exploited vulnerabilities that in some cases dated back to 2018. Security patches were released. But many telecommunications companies never applied them. The regulatory structure that might have compelled them to do so did not exist, and the consequences of that gap were felt not by the companies but by the governments and citizens whose communications ran through their networks.
The geopolitical dimension of all of this means that the threat is not going to recede when the news cycle moves on. Salt Typhoon is still being investigated. In February 2026, Senator Maria Cantwell sent a letter to the Senate Commerce Committee requesting an oversight hearing with the CEOs of AT&T and Verizon after both companies refused to share security assessment documents with Congress, blocked Mandiant from cooperating with congressional requests, and declined to provide specific documentation corroborating their claims that the intrusion had been contained.

The answer to that question matters not just for those two companies but for every organization whose infrastructure touches theirs. Because in a supply chain attack, the target and the victim are not always the same entity, and that gap is exactly where nation-state actors continue to operate. And as long as the institutions responsible for critical communications infrastructure can decline congressional oversight requests on the grounds of attorney-client privilege while 265 million customers remain on networks whose security posture is unverified, the governance gap that makes supply chain warfare so effective will remain open.