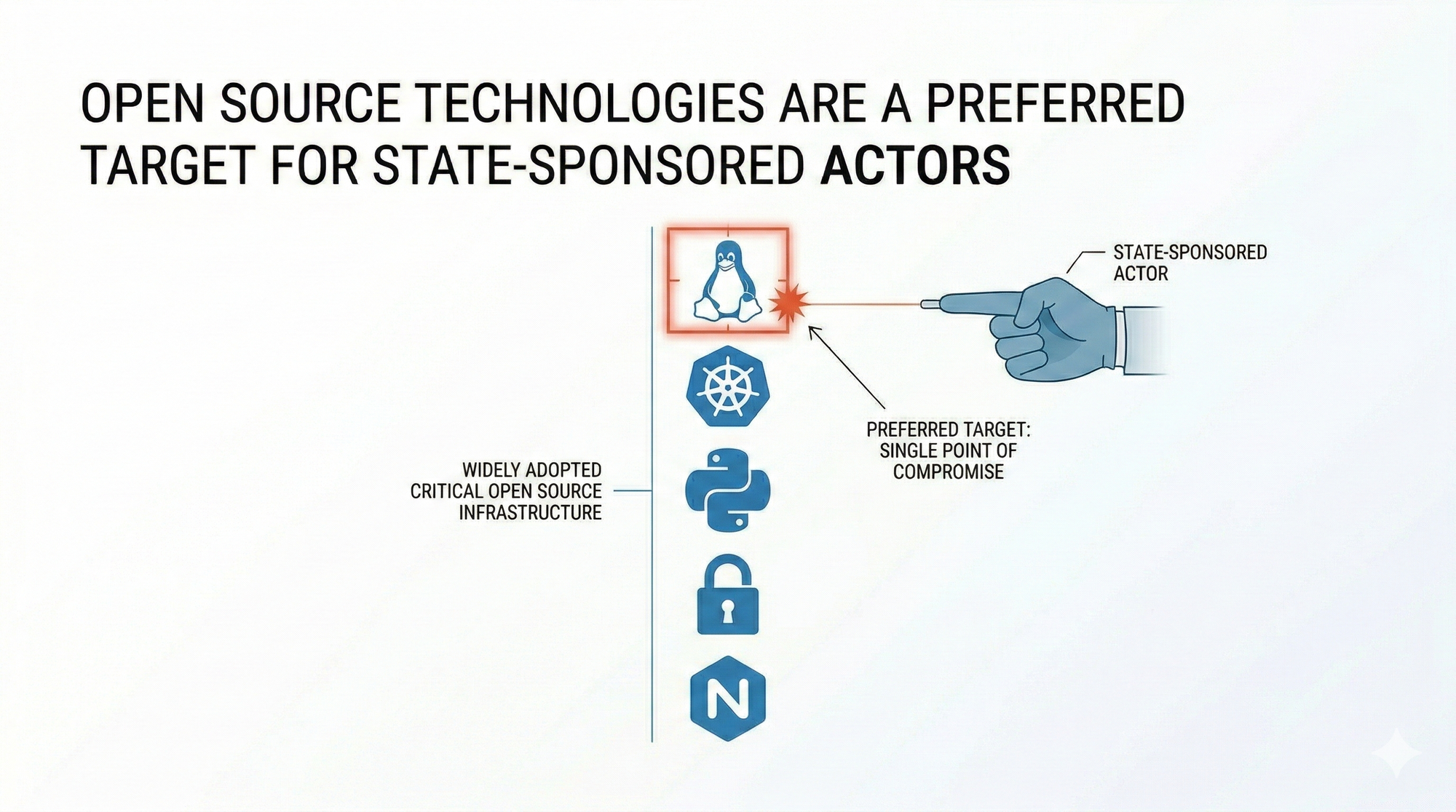
Open source software powers the majority of the world's critical infrastructure. Linux runs the servers, Kubernetes orchestrates the containers, OpenSSL handles the encryption, and the sprawling dependency ecosystems of Python and Node.js underpin applications across financial services, healthcare, energy, and government simultaneously. That reach is the direct result of open source doing precisely what it was designed to do: producing reliable, inspectable, collaboratively maintained software that any organization can adopt, audit, and build on without a licensing agreement or a vendor relationship.
But the same properties that make open source software trustworthy and operationally valuable for the organizations building on it also make it strategically attractive for the adversaries targeting them, and state-sponsored actors with broad collection objectives have been systematic about exploiting that value in ways that the industry has been slower to reckon with than the incidents themselves would warrant.
For state-sponsored actors, the question is not whether to target open source infrastructure. It is which vulnerability in which project reaches the most high-value environments simultaneously.
The Attack Surface Is Public and Permanently Readable
Targeting proprietary software requires adversaries to invest significant resources in reverse engineering the product before they can understand where it breaks, which creates a natural barrier between vulnerability discovery and exploitation that does not exist in open source environments. Open source software removes that barrier entirely, because the source code is readable by anyone, the dependency chains are documented in public package manifests that map exactly which libraries each project depends on, and the vulnerability disclosures are filed in public CVE databases and tracked in public security advisories the moment they are confirmed by the maintaining community.
When a critical vulnerability is discovered in a widely used open source library, every organization running that library becomes a potential target at the same moment, and adversaries know who those organizations are because the dependency is publicly documented in the same repositories that developers use to build their applications. The Log4Shell vulnerability disclosed in December 2021 demonstrated this dynamic at a scale that made its strategic implications impossible to ignore, because Log4j was embedded across thousands of enterprise applications, government systems, and critical infrastructure platforms in dozens of countries, and within hours of the CVE being published, state-sponsored groups attributed to China, Iran, North Korea, and Russia were observed actively scanning for vulnerable systems. Those actors did not need to discover the vulnerability before defenders did, because the public disclosure gave adversaries and defenders identical starting information, and the decisive advantage was simply the ability to move from that disclosure to active scanning faster than most organizations could complete an initial assessment of whether they were even affected.

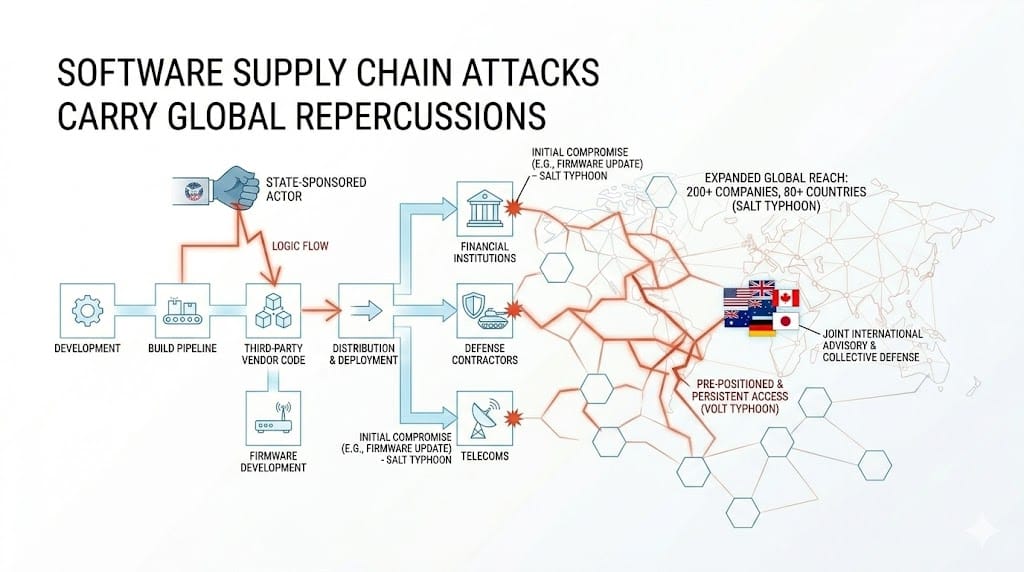
Supply Chain Access as a Force Multiplier
Targeting an individual organization requires intelligence about that organization's specific infrastructure, its network architecture, its software stack, and the people who maintain it, all of which demands significant resources and carries a meaningful risk of detection before exploitation is complete. Targeting a widely adopted open source project offers something considerably more efficient: potential access to every organization running that project, across industries and jurisdictions simultaneously, through a single point of compromise that propagates outward through trust relationships the targets themselves established by choosing to depend on that software.
The XZ Utils operation uncovered in 2024 illustrated exactly how far state-sponsored actors are willing to invest in that kind of supply chain access, because the threat actor behind it spent nearly two years building a fabricated identity within the open source community, earning the trust of maintainers through consistent and competent contributions before introducing a carefully concealed backdoor into the codebase of a compression library present in most Linux distributions globally. The operation came within a single developer's curiosity of reaching production deployments across a significant portion of Linux-based critical infrastructure worldwide, and what made it possible was not a technical breakthrough but a patient, methodical exploitation of the trust model that open source communities depend on to function, because contributor access is earned through demonstrated reliability rather than verified identity.

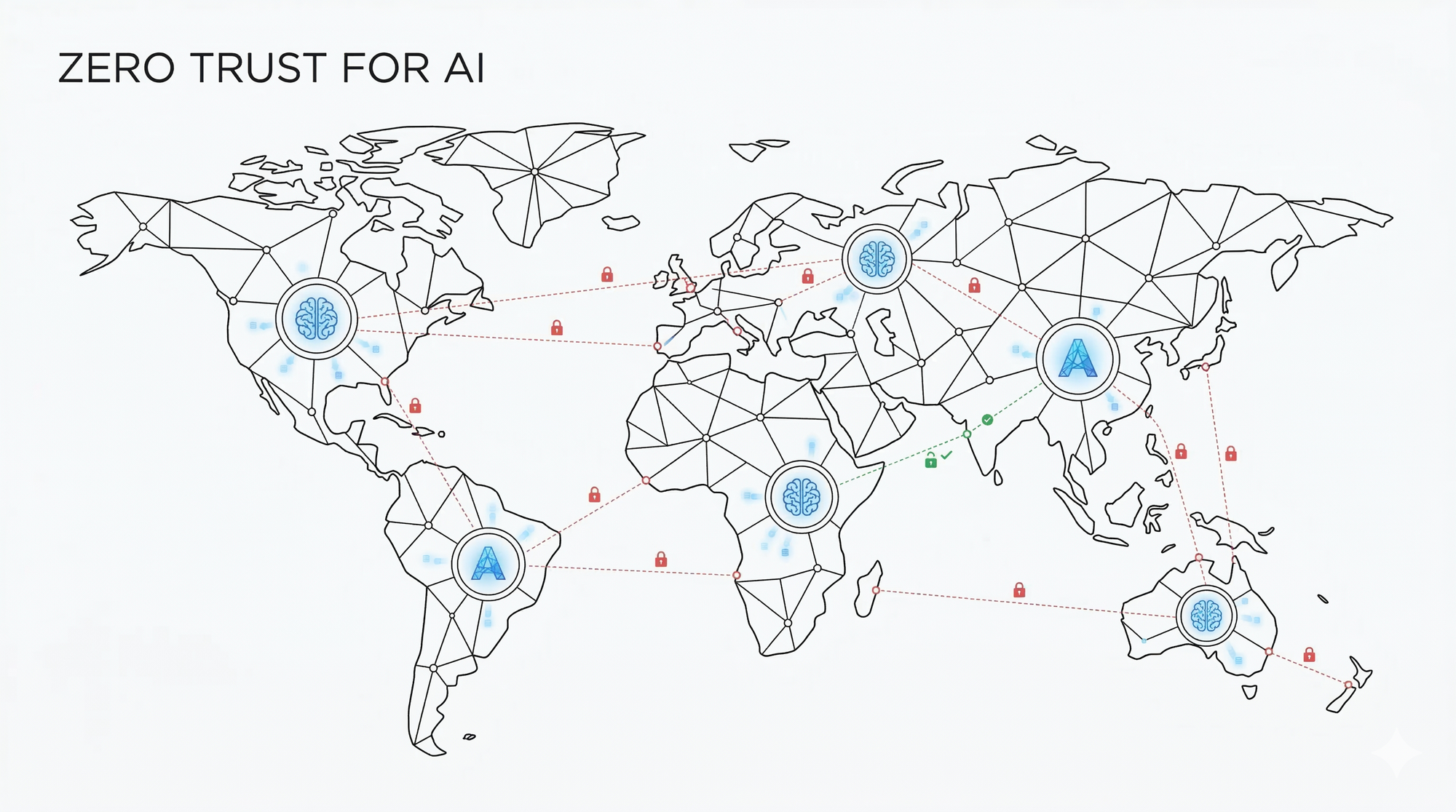
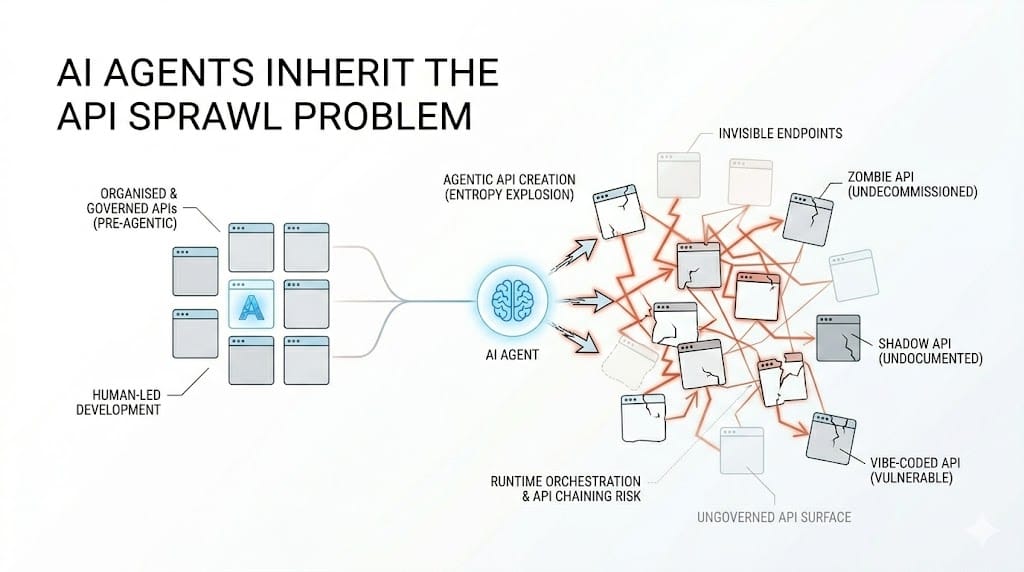
Container infrastructure compounds this exposure further, because containerized applications are built on layered open source base images that inherit every vulnerability present in their upstream dependencies, and those applications expose their functionality through APIs that extend the blast radius of any successful exploitation outward through every service integration built on top of them. [Read: Container Infrastructure Is a Shared Global Attack Surface] The open source dependency chain and the container supply chain are the same attack surface approached from different angles, and a compromise at any layer of that stack propagates into every environment that built on top of it.
The Speed Asymmetry That Defines the Risk
The structural advantage that state-sponsored actors hold in open source targeting is not primarily a technical one, because the defenders and the adversaries frequently have access to the same vulnerability research, the same CVE databases, and the same understanding of how a given exploit works. The advantage is operational and it comes down to the difference between how long it takes an adversary to move from a public vulnerability disclosure to active exploitation and how long it takes a defender to move from that same disclosure through vulnerability assessment, change management approval, testing, and deployment across a distributed production environment, all while managing every other operational priority that did not stop because a new CVE was filed.
Organizations that patch consistently and quickly close that window and reduce their exposure to the specific class of opportunistic exploitation that open source targeting depends on, but across critical infrastructure sectors where patching requires coordinated maintenance windows, regulatory approval processes, or careful validation against complex downstream dependencies, the window stays open long enough for actors who are monitoring public feeds and moving immediately to operate inside it at scale and with strategic intent.
What Running Open Source Infrastructure at Scale Actually Requires
Moving away from open source is not the answer and is not a realistic option for most organizations running critical infrastructure, because the software that powers that infrastructure is open source for reasons that remain valid: it is reliable, it is auditable, it is maintained by communities whose collective expertise exceeds what any single vendor can assemble, and its transparency is genuinely valuable for defenders who need to understand exactly what is running in their environments. But organizations running open source infrastructure at scale need to treat public vulnerability disclosures as operational events that trigger an immediate response rather than maintenance items that enter a patching queue on a regular cycle.
Monitoring CVE feeds for the specific libraries and base images present in production, maintaining accurate software bills of materials so that the blast radius of any new disclosure can be assessed within hours rather than days, and automating rebuild and redeployment pipelines where the operational environment permits it are the practices that close the speed gap that state-sponsored targeting depends on. They do not eliminate the targeting, because nothing will make open source infrastructure invisible to adversaries who are reading the same public repositories that developers use, but they reduce the window inside which that targeting can be converted into a successful exploitation before the affected organization has even confirmed it is vulnerable.